
File Transfer & Information Security Blog
Featured Articles
-
What is Extreme File Transfer (XFT)?
There is a growing trend in the data transfer arena. What is extreme file transfer and why is there an increasing need for it?
-
How to Use PowerShell to Monitor REST APIs
This article explains how to use PowerShell to monitor REST APIs.
-
The GDPR and US Data Protection Regulations Diverge
There are some serious difficulties ahead for businesses in the wake of the repeal of the US Internet Privacy Bill. How can US businesses comply with the GDPR?
-
Reducing Security Breaches in Fintech is a Business Priority
Fintech is a valuable target for hackers seeking financial reward and we can’t stop all breaches without changing our attitude towards security.
-
What is Pester for PowerShell?
As you begin to depend on your PowerShell scripts for more important tasks, you'll discover that building tests for those scripts become necessary.
-
Data Privacy Dead After FCC Reversal Legalizes ISP Data Mining
The repeal of the FCC rule on ISP data mining has serious implications, not only for individual data privacy, but for businesses as well.
-
Manage DNS Zones with PowerShell
If you find yourself making changes on your Microsoft DNS servers using the DNS MMC snapin you're probably wasting a lot of time.
-
Data Privacy: 5 Steps to Prevent Security Breaches
Assuring data privacy has been a hot issue for years and the basic building blocks of a strong defense against cybercriminal data theft hasn't changed.
-
What is Infrastructure Testing?
As we all try to do more with less with automation, we sometimes get to a point to where we've got a new problem. We're now running so many scripts and processes that, in the end, we're not sure what "done" looks like.
-
Select-String: The grep of PowerShell
When writing PowerShell code and you need to search for text inside of a single string or an entire text file, where do you turn?
-
File Cannot Be Accessed Fix with Handle.exe
Handle.exe is a 3rd party tool that can help track down a process that is locking down a file you are trying access. Here is how.
-
5 Tips IT Managers Can Use to Protect Sensitive Data
Sophie Pellissier | | Security
Sophie Pellissier of Ipswitch looks at 5 facts IT managers should be aware of to protect sensitive data.
-
Working with File Catalogs in PowerShell 5.1
Working with lots of files all strewn about in different folders can sometimes prove troublesome. This is where PowerShell can help.
-
837 Claims – 835 Remit Optimization
Want to know how healthcare IT organizations can best prove their worth to the business? Optimize the 835 Remit and 837 Claim process so there are fewer rejections, clarifications, missed files and delays.
-
Robust IT Infrastructure for Lean IT Departments
Lean IT, in its essence, is all about doing well the IT tasks the organization needs to do, while not doing things that don't really need to be done.
-
How Financial Services Firms Can Prevent SLA Penalties
For 95 percent of enterprises, one hour of downtime costs $100,000 or more in SLA penalties according to data from ITIC.
-
Deep Web Monitoring and the Future of Data Breach Detection
Greg Mooney | | Security
If you're like me and have a knack for cyber security trends, you will find yourself having many sleepless nights. Our lives and data is are the internet for the taking and the weakest link in finding compromised data is knowing it's been compromised in the first place.
-
A Day in the Life of a Healthcare CIO — No Pressure!
Some things happen to a healthcare CIO that just don't happen to IT execs outside of the healthcare industry. On some days, you walk down the hospital corridors beaming, thinking of how your work directly improves human health and quality of life. On other days, you'd...
-
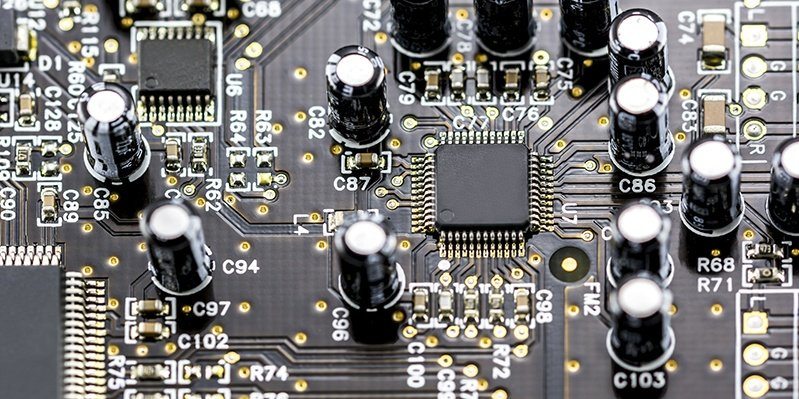
Fixing Blown Capacitors for Hero Status
A lot of people throw away a lot of otherwise fully operational electronics due to blown capacitors (caps). I've worked in IT for quite a few years and that doesn't even include my 5 years of time in the audio consumer electronics space. To put is simply, a capacitor is...