
File Transfer & Information Security Blog
Featured Articles
-
How To Enumerate Windows User Profiles With PowerShell
When trying to list all profiles, you need a script that can account for a variety of scenarios.
-
4 Important Factors Of Biometrics In Banking
Kathleen Burns | | IT Insights
Biometrics are infiltrating the financial industry. As the digital age expands, it is important to find a balance between security and accessibility.
-
IT Pros, Do You Have Cybersecurity On Your Resume?
Jeanne Hopkins | | IT Insights
Experience and knowledge in cybersecurity have become a necessary resume addition for anyone pursuing a career in the IT field.
-
Creative Ways to Keep Your Server Room Cool
No need heavy-jacket temperatures, but you also shouldn’t start sweating the moment you enter!
-
Should You Be Concerned About Your Online Banking Security?
Online and mobile banking are on the rise, but we need to understand what the stakes are for the protection of our personal information.
-
Immutable Buckets: An Essential Data Protection Tool
If you need some serious protection on your data, creating an immutable bucket may be your best option.
-
What Might Be Missing From Your PCI Security Program?
Sometimes simple compliance isn't sufficient. Information security is complex and can demand a lot of attention.
-
Branding In Healthcare: A Strong Brand Builds Trust
Jeanne Hopkins | | IT Insights
In the healthcare industry, developing a strong brand will put you ahead of the vast majority of your competition.
-
How AI is Helping the Finance Industry Prevent Fraud
Kevin Howell | | Security
Fintech companies, like PayPal, are using machine learning to prevent fraud. It's only a matter of time until AI consumes the finance industry.
-
How To Properly Protect Data With FTPS
FTPS helps to encrypt and transfer private information within the constraints of regulatory requirements.
-
Branding in Healthcare: 5 Reasons You Need a Strong Brand
Jeanne Hopkins | | IT Insights
In the old days of healthcare, who needed a brand? People came to you because you were there, not because they deliberately chose you over some alternative.
-
Working with Windows Services in PowerShell
PowerShell helps free up time by taking over certain service management tasks. See how to create such tools here.
-
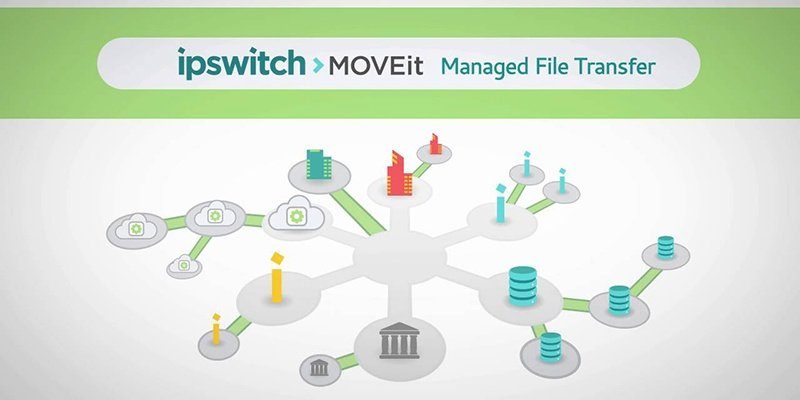
MOVEit 2017 Plus Enhances Security with Multifactor Authentication (MFA)
Introducing the new and improved MOVEit 2017 Plus. MOVEit 2017 Plus adds important security features, such as multifactor authentication.
-
Free up PC Space by Automating Temporary File Cleanup
In this tutorial, we cover how to quickly and easily cleanup all the "junk" that accumulates on PCs by automating in PowerShell.
-
Could Blockchain Ensure Financial Data Security?
Blockchain is rapidly increasing its reputation as a mechanism for faster payment services and greater data security.
-
5 Tips for using Google Apps and File Sharing Services in Healthcare
Shelling out the cash for business and healthcare versions of file sharing services grants you worthwhile visibility, control, and encryption abilities for PHI.
-
Securing Digital Communications Using a PKI
Just how protected are your passwords and credit card numbers when you enter them into websites? That's where PKI (public key infrastructure) comes in.
-
What is TFTP (Trivial File Transfer Protocol)?
What exactly is TFTP (Trivial File Transfer Protocol) and how does it differ from other file transfer tools?
-
Deploying MalwareBytes Anti-Malware Utility with PowerShell
Here is how you can deploy MalwareBytes, a popular anti-malware tool, quickly and inexpensively on multiple machines at once with PowerShell.